The essential penetration testing tools, all in one place
Pentest-Tools.com is a comprehensive toolset for offensive security testing, focused on web applications and network penetration testing.
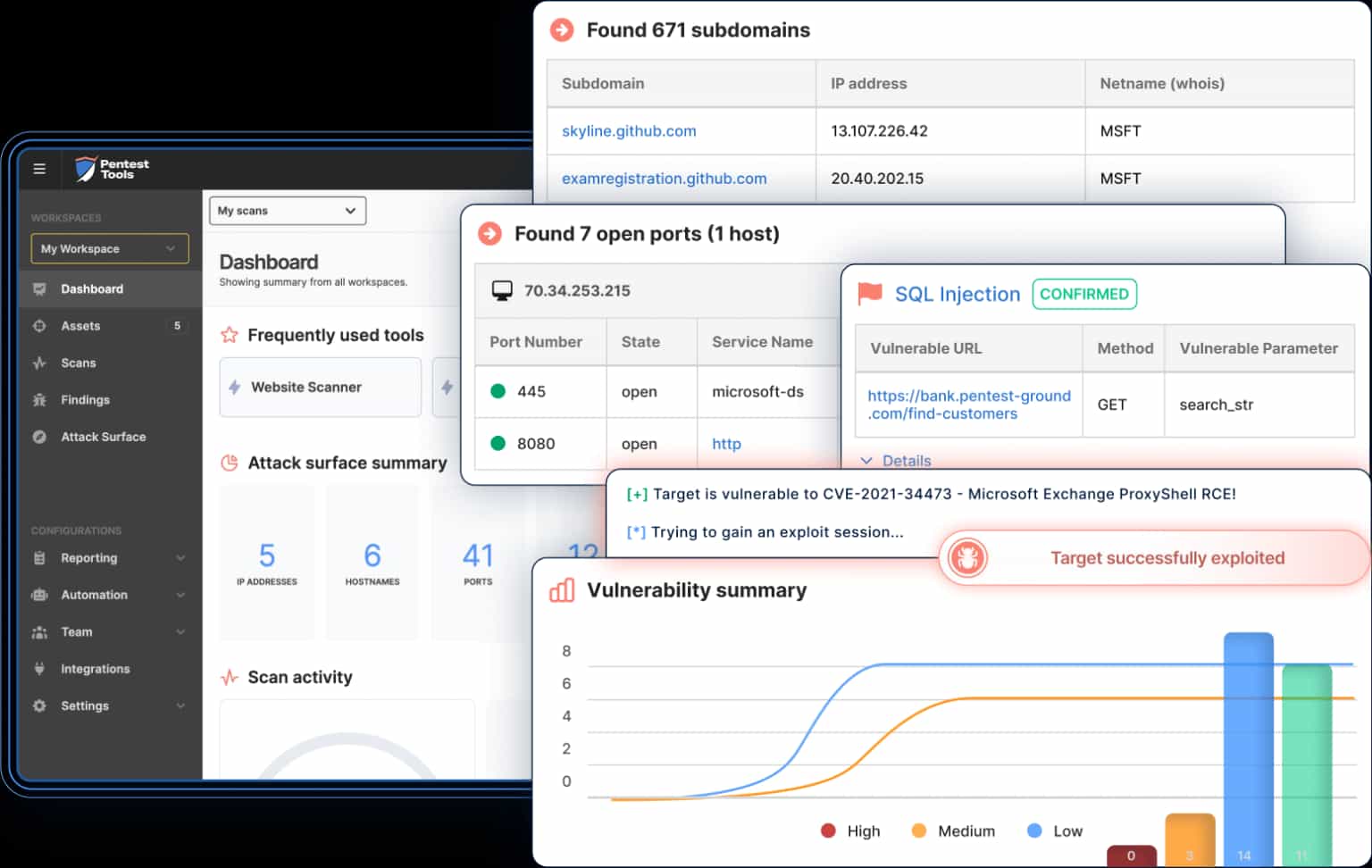
Discover & exploit vulnerabilities
Aggregate findings into pentest reports
Continuously monitor assets
Trusted by 1,500+ security teams in 95+ countries





What you can do with Pentest-Tools.com
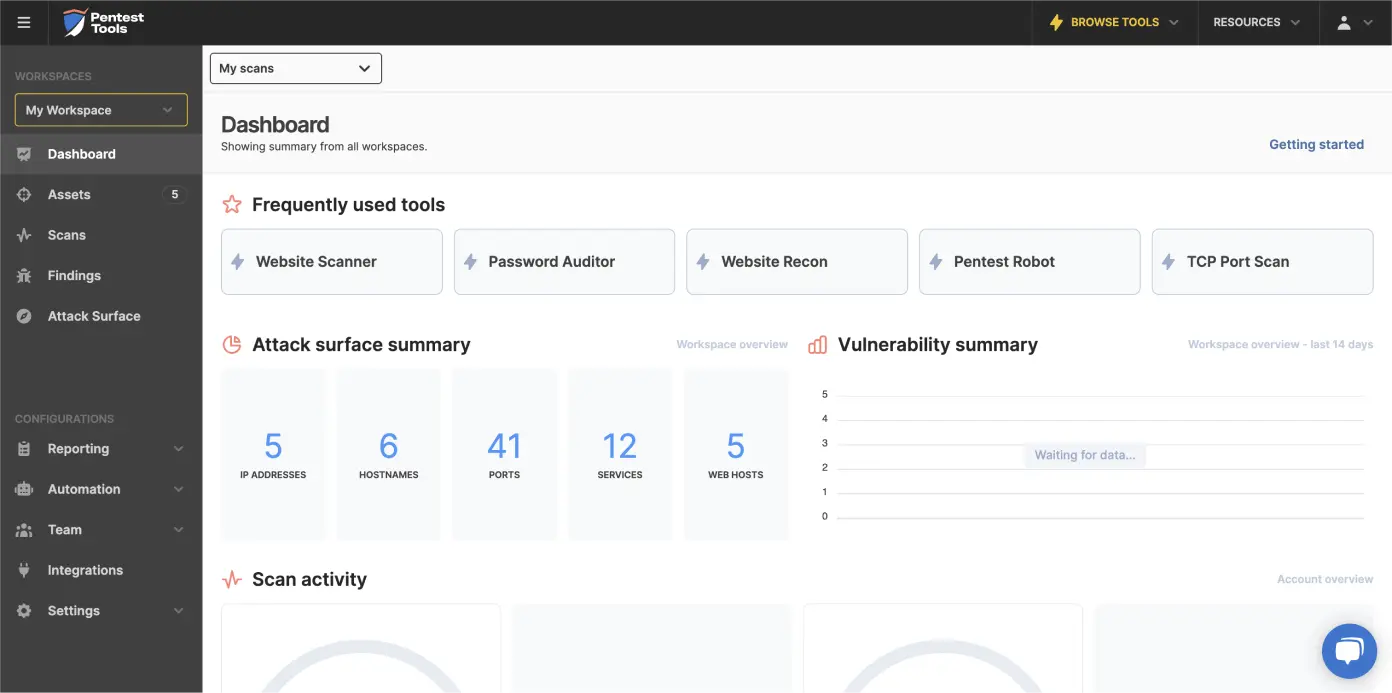
Built by a team of experienced penetration testers, Pentest-Tools.com is a web-based platform that speeds-up the common steps performed in almost every assessment: reconnaissance, vulnerability scanning, exploitation, and report writing. Using the 20+ built-in tools, you get quick insights into target's weaknesses so you know where to dig deeper, pop shells, and have fun.

Attack Surface Mapping
Discover the attack surface of your network targets, including subdomains, open ports and running services
Map web application technologies, take screenshots, detect WAFs and discover hidden files by fuzzing
Popular tools: Subdomain Finder, TCP Port Scanner, URL Fuzzer

Vulnerability Scanning
Web Application Scanning
Use our powerful, custom Website Vulnerability Scanner to accurately detect common vulnerabilities (e.g. XSS, SQLi, OS Command injection) in classic and modern web applications (SPAs)
Quickly identify specific security issues with dedicated scanners for API vulnerabilities and widely used CMSs (Wordpress, Drupal, Joomla, Sharepoint)
Network Scanning
Uncover a wide range of infrastructure security issues with our Network Vulnerability Scanner, a custom tool which finds unnecessary open ports, missing security patches, service misconfigurations, and critical CVEs (Log4shell, ProxyShell, etc.)
Find weak credentials and prove the risk of unauthorized access with our Password Auditor tool

Exploitation
Exploit critical CVEs, gain initial access, extract sensitive files and more with Sniper - Auto Exploiter
Show your customers the real impact of your findings by extracting powerful evidence and creating strong proof-of-concepts
Also exploit web vulnerabilities like SQL injection, XSS and more, extracting data to demonstrate real security risks

Writing Pentest Reports
Use the Pentest Report Generator to quickly create editable Word (.docx) reports from your findings – 50% faster than the manual way
Simplify report writing with predefined Word templates and a rich library of common findings (with description, risk, and recommendations)
Create your own custom, reusable findings and report templates

Continuous Security Monitoring
Schedule periodic vulnerability scans
Automatically send reports to Email, Slack or Webhooks
Get notified when high risk issues are found or when other custom conditions are met
Pentest-Tools.com - Platform Overview
Pentest-Tools.com is for
Offensive Security Teams
Save time for more creative hacking
- Quickly map the attack surface of your target
- Run fire-and-forget vulnerability scanners (web and network) to discover low-hanging fruits
- Validate critical CVEs through safe automatic exploitation
- Generate editable pentest reports (Word .docx) from your findings
- Test from different geo locations using VPN tunnels
- Automate recurring tasks to gain more time for manual analysis
- Work collaboratively with your colleagues and keep engagement data in one place
Defensive Security Teams
Assess and monitor your security posture
- Run web application vulnerability scans (also logged-in)
- Scan for network vulnerabilities (missing patches, misconfigurations, etc.)
- Continuously run asset discovery and find shadow IT
- Schedule periodic scans to monitor for security issues
- Scan both internal apps and public-facing assets
- Automatically send results to Email, Jira, Slack, Webhooks, and more
- Use the API to integrate the scanners into your workflow
System builders & admins
Speed up routine security checks
- Run basic security hygiene checks and export simple reports
- Perform and automate security compliance scans
- Assess your security posture before external audits
- Check for misconfigurations in web servers and applications
- Discover missing patches on servers and workstations
- Automatically send results to Email, Jira, Slack, Webhooks, and more
- Get notified when security issues emerge in your environment
We're hard at work right now!
- 360 000
- Scans last month
- 875 000
- Subdomains discovered
- 290 000
- Open ports detected
- 10 700
- High-risk vulnerabilities found
You're backed by a strong team
Pentest-Tools.com was created in 2013 by a team of professional penetration testers which continue to guide the product development today and push for better accuracy, speed and flexibility.
We use our practical experience and industry knowledge to improve Pentest-Tools.com with new security testing techniques, better workflows, and detections for the latest vulnerabilities. All of this to help our customers deliver more value with their security tests.

The Pentest-Tools.com team at DefCamp 2022
What's unique about Pentest-Tools.com
Our platform is a one-of-a-kind solution in the offensive security space because it combines 20+ tools and features to streamline the entire security testing workflow. Plus, it’s very easy to feed the tool results into professional reports, saving you hours of tedious work. Enjoy the rest of your free time!
Our Security Research Team constantly updates all the tools with detections and exploits for new, critical vulnerabilities
We battle test our tools in live pentesting engagements, which helps us fine tune their settings for the best performance
Customer testimonials
Pentest-Tools.com is the Swiss army knife for anyone performing black-box external network security assessments and an all-in-one comprehensive toolset for external red team/asset mapping engagements. I used to rely on a wide range of tools when mapping and scanning external organization assets, but since I found this comprehensive solution, I rarely need to use more than one.
Shay Chen
CEO at Effective Security Ltd.
Israel 🇮🇱

We don't replace the humans in the loop
Pentest-Tools.com doesn’t replace skilled security pros with automation.
Instead, our toolset amplifies your abilities with more effective workflows. We save infosec experts time so they can excel at creative hacking, custom testing, security research, and community contribution.
Technology vetted by industry pros

Deloitte Technology Fast 50 CE
Selected in Companies to Watch

G2 2022
Winter leader - Penetration Testing

SC Awards 2022
Best Vulnerability Management Solution (highly commended)







