SQL Injection Scanner
Technical details
What is an SQL injection and how do I prevent this attack?
SQL Injection remains one of the most prevalent attacks used by hackers and a serious security threat to both individuals and companies.
SQLi is also one of the most well-known web application vulnerabilities with a dedicated chapter in the OWASP Top 10 project and is also a highly chased after vulnerability in bug bounty programs.
A common SQL injection attack happens when attackers try to insert malicious SQL statements located in an HTTP (or HTTPS) request by changing the current behavior of SQL statements created by the web application.
They do this by first finding a vulnerable user input within a web app and create input content which is often used as the malicious payload to launch this attack. The input provided by an attacker may include characters that could interfere with the SQL syntax and will result in arbitrary SQL queries performed on the database.
As a result, the risk of an SQL Injection vulnerability is that the attacker could:
- Read/write information from the database
- Read/write files from the disk (under certain conditions)
- Execute operating system commands on the database server (under certain conditions)
Here is a sample URL which extracts the type and version of the database server (MySQL) by exploiting the SQL Injection vulnerability: http://vulnapp.example.com/travel.jsp?id=x' UNION SELECT NULL, NULL, @@version -- '
One of the most common types of SQL injection techniques is error-based SQL injection which is the simplest SQL exploit and easy to detect. It involves using classic HTTP requests by inserting unexpected commands through a user interface to cause the database server to respond with an error that includes information about the target: structure, version, or operating system.
In the below example, an SQL command has been inserted to change the value of the fields Username ($username = 1' or '1' = '1) and Password ($password = 1' or '1' = '1) which will be modified as follows:
- Username
(($username = 1' or '1' = '1') LIMIT 1/*) - Password
($password = foo)
This is an example of a URL with a modified query that will generate an error and let a malicious hacker gain access to all the usernames and passwords. http://www.example.com/index.php?username=1'%20or%20'1'%20=%20'1'))%20LIMIT%201/*&password=foo
To prevent this from happening, you should avoid using the user input directly in the application code. Developers need to sanitize the input section and remove the potentially malicious code in SQL statements that could allow attackers to gain unauthorized access to sensitive database information: usernames, passwords, and other essential credentials.
Prevention is always the best cure, and you can simply detect web application vulnerabilities by using our online scanner.
How does the SQL Scanner work?
To better secure your web applications from SQL injection attack is to identify and fix security vulnerabilities before malicious hackers do.
We created this SQL injection scanner to make it easy for you to perform SQL injection testing and find web applications flaws much faster.
The SQL Injection Scanner is our comprehensive online security testing tool for infosec specialists. It helps you do a complete SQL injection assessment of your target web applications and find critical vulnerabilities with a significant business impact.
The online tool provides an intuitive and simple interface.
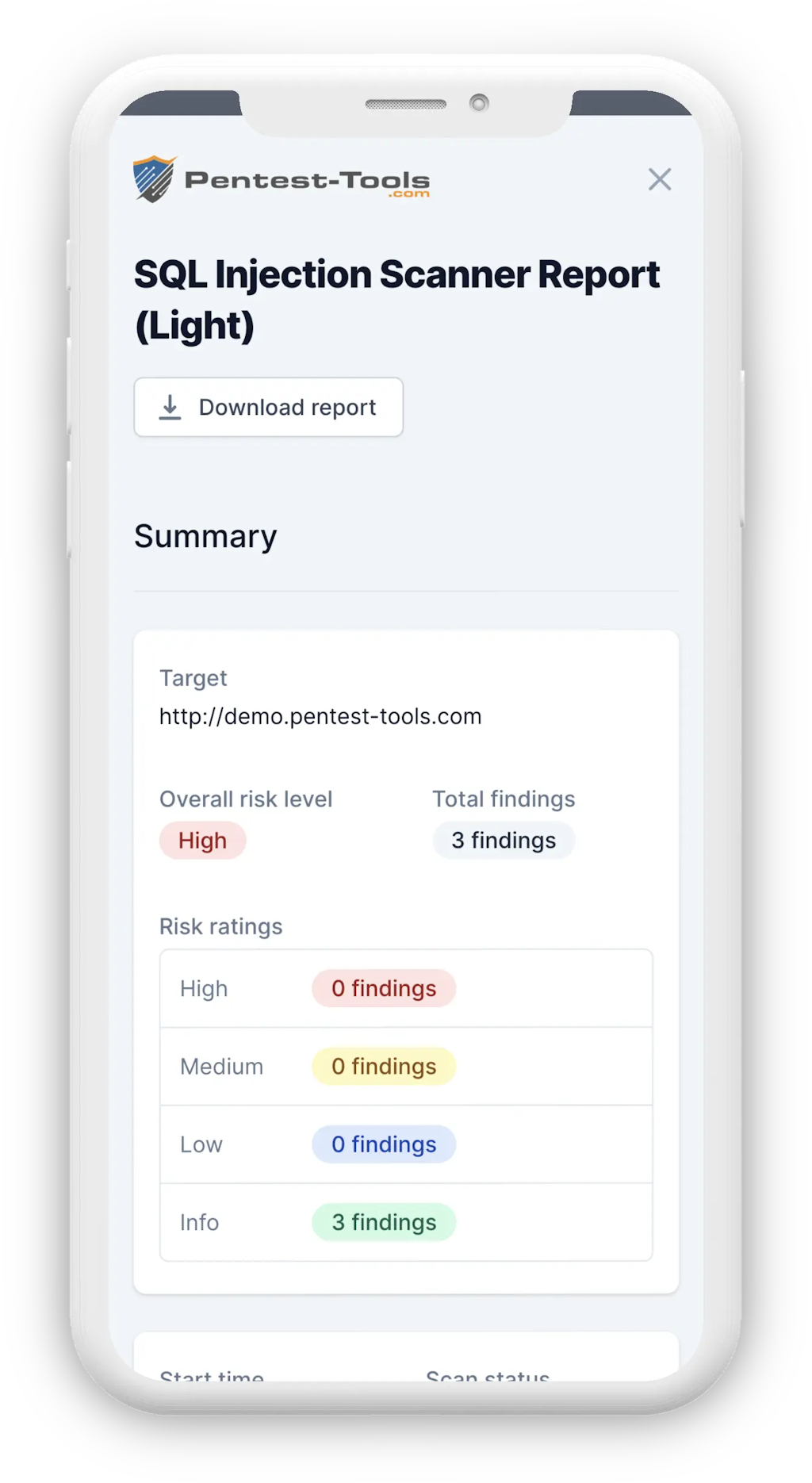
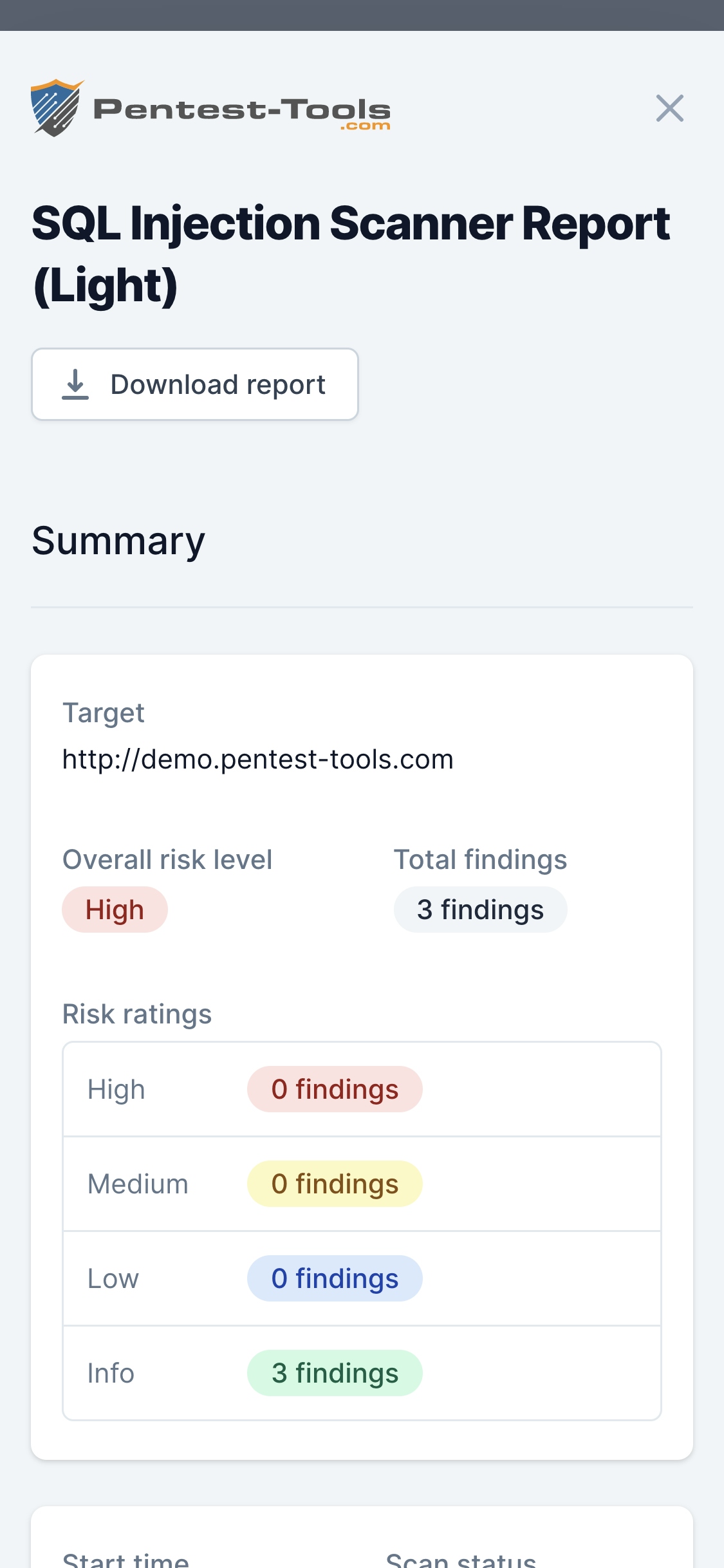
The SQL Injection Scanner (Light Scan) performs a quick and fast scan of a target URL that allows it to identify vulnerabilities in web applications. It does this by validating if the parameters of the target URLs are vulnerable to SQL Injection and then reports the malicious pages that could affect the target website.
The online scanner includes two steps:
- Spidering the target: In this first step, the scanner tries to identify all the pages within the target web application, including injectable parameters in login forms, URLs, headers, etc.
- Accurate SQL injection testing: During this phase, for each page discovered in the previous step, the online tool will try to detect if the parameters are vulnerable to SQL Injection and report them in the results page.
The table below shows the differences between the Light scan and the Full scan:
| Scanner capabilities | Light Scan | Full Scan |
|---|---|---|
| Spider max URLs | 20 | 500 |
| Spider max duration | 1 minute | 15 minutes |
| Active scan max duration | 2 minutes | 30 minutes |
Warning: The SQL Injection tool generates some HTTP requests that can be flagged as attacks on the server side (although they are harmless). We recommend not to perform an SQL injection test if you don't have permission or proper authorization from the owner of the target web app.
Will this tool also check for MySQL Injection?
MySQL is one of the most accessible and widely deployed SQL databases running on websites and systems and also the top target for attackers. They will search for vulnerable user inputs within the MSQL databases, inject malicious code to manipulate them and get unauthorized access.
Our online tool scans the target URL containing SQL commands and checks if the MySQL database has been exposed to any SQL injection vulnerability. It can perform a full SQL injection assessment of the target web application to detect vulnerabilities to mitigate before being compromised.
Other popular relational database management systems (RDBMS) that are vulnerable to SQL injection are Microsoft SQL Server, Oracle, or SQLite.
Parameters
| Parameter | Description |
|---|---|
| Target URL | This is the URL of the website that will be scanned. All URLs must start with http or https. |
| Light Scan | This scan is faster but less comprehensive than the full scan. |
| Full Scan | This is a complete SQL Injection assessment of the target web application. |
How it works
The tool can do an SQL injection test by inserting special characters (eg. ', ", 2*3) in all input fields of the target application and monitoring the web page's behavior. If it finds database errors on the website, this indicates a potential SQL Injection attack scenario.
In order to validate the vulnerability found, the SQL Injection scanner attempts to construct a syntactically correct SQL query that demonstrates the injection was successful. That is why the following results will be displayed: http://vulnapp.example.com/bookings.php?cat=4 AND 1=1 --
The SQL Injection scanner does not attempt to exploit SQL injection, it simply detects the presence of any vulnerability that could affect your backend database. If flaws are detected, our online tool offers detailed information about the risks you are exposed to and recommendations on how to perform an effective remediation process. Start scanning for web applications vulnerabilities today to avoid being exposed to SQL Injection attacks which let malicious hackers tamper with sensitive information (e.g. usernames, passwords, and other essential credentials) by disclosing, deleting , or keeping it for ransom.
For more in-depth information about SQL Injection attacks, including how to remediate vulnerabilities that make them possible, check out the OWASP SQL Injection Page.