Features of Pentest-Tools.com
A cloud-based pentesting platform built to make your workflow easier and smoother
Explore the features our customers use in their pentesting engagements and get inspired to try a subscription out for yourself and your team.
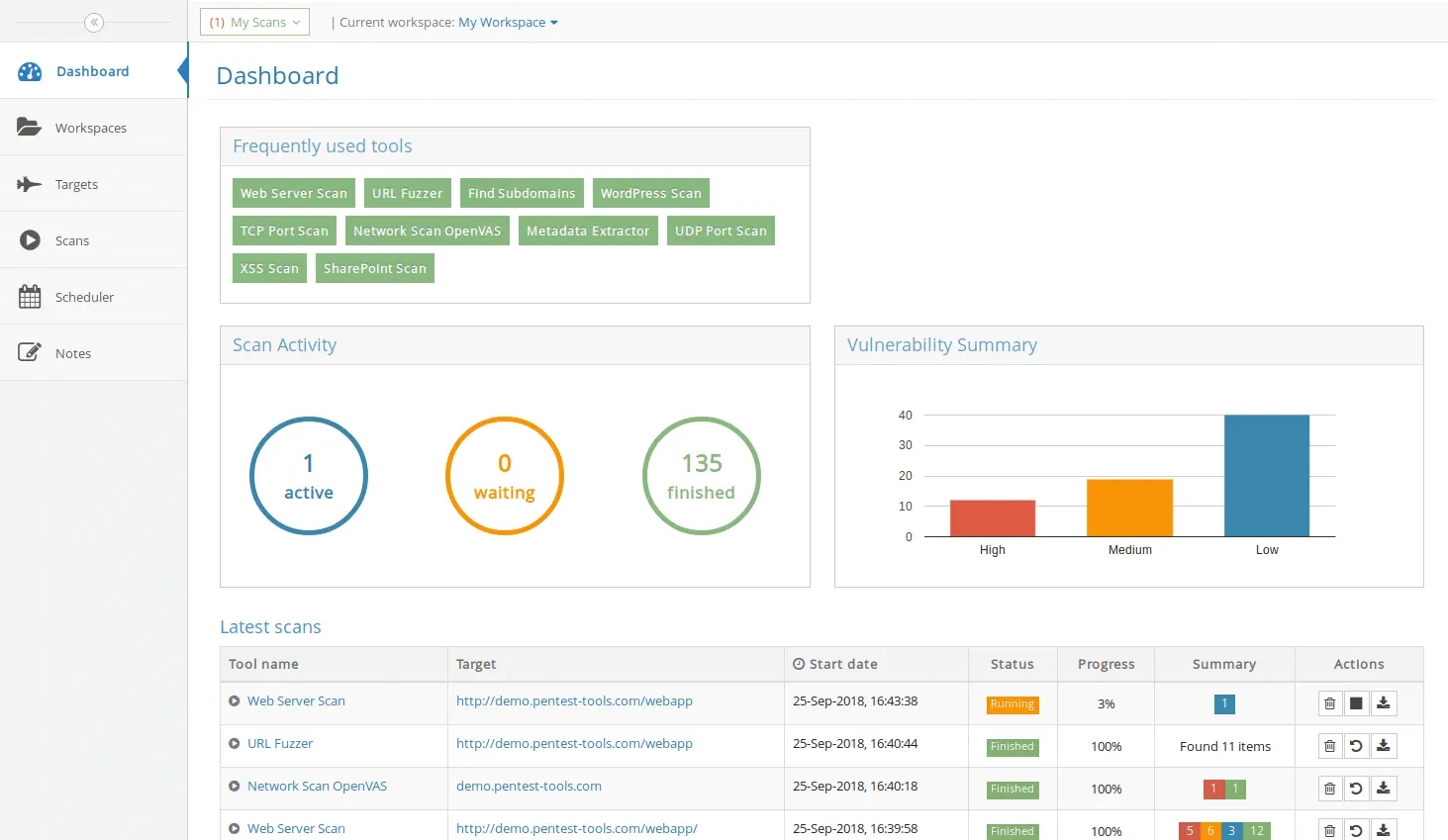
Visualize your scan results in the Dashboard
The Dashboard gives you an overview of your scan results. The all-in-one place to visualize your scan activity, a graphical summary of vulnerabilities found, and the list of your latest scans.
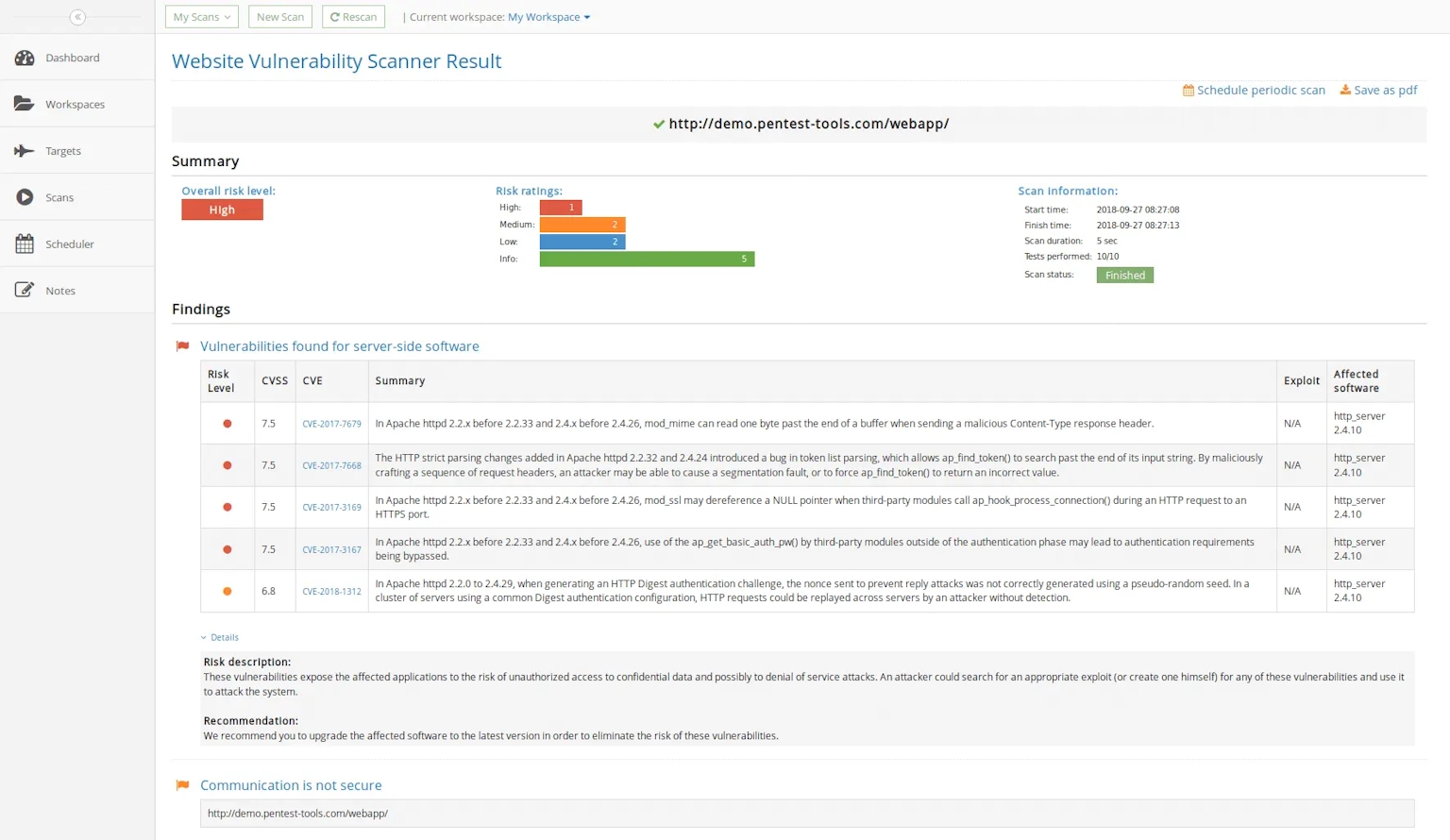
Detailed pentesting reports
We focus on making the reports as friendly and human-readable as possible. Each tool report starts with a visual summary of the results and continues with the Findings section. Here you can find details about vulnerabilities found, including description, evidence, risk, and recommendations for fixing them.
With the White label feature, you can customize your pentesting reports and add your brand company's logo name instead of the Pentest-Tools.com one.
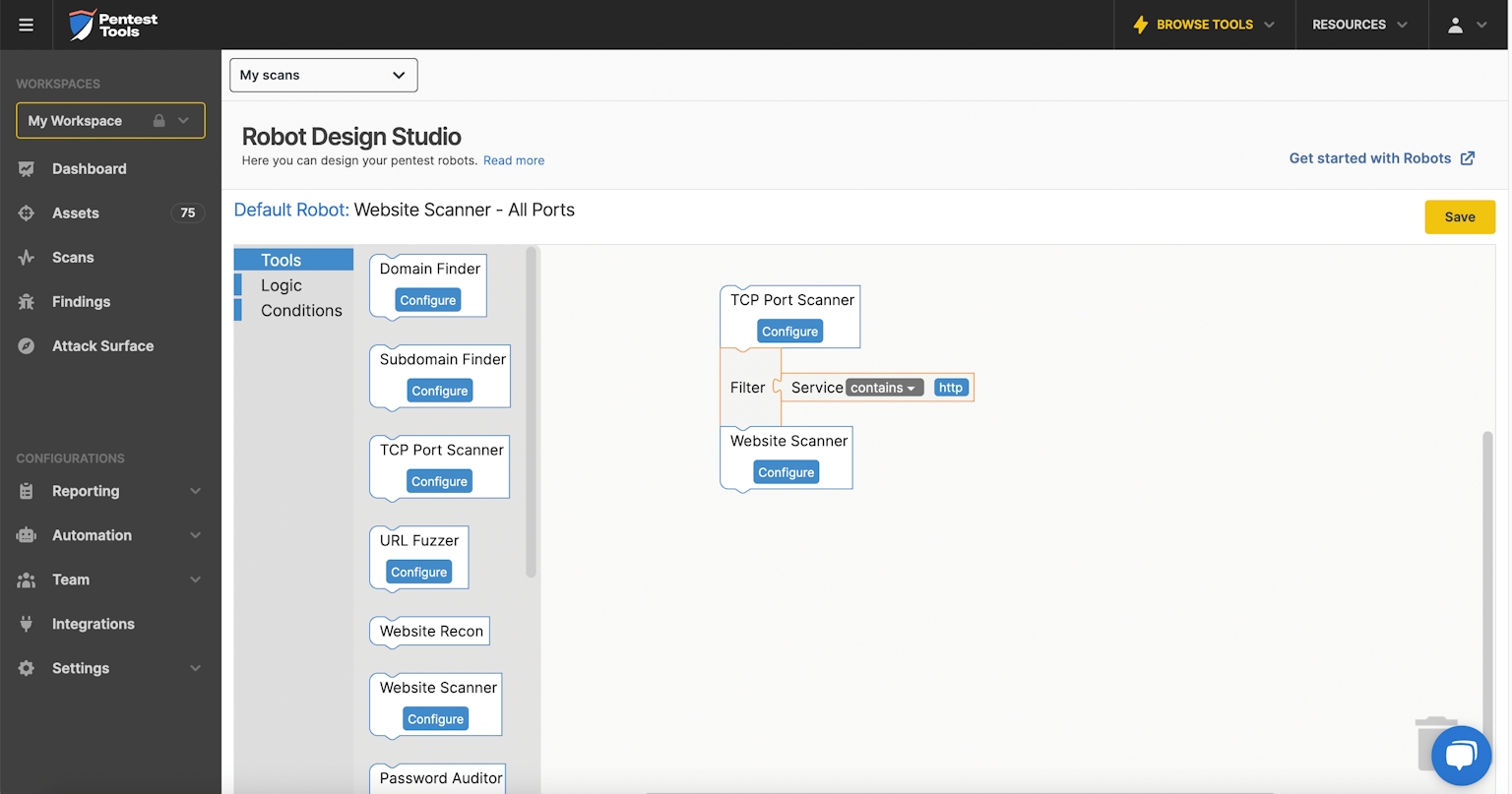
Automate 80% of your manual pentesting work with Pentest Robots
Pentest Robots are software robots (bots) that orchestrate the tools on Pentest-Tools.com. Use Pentest Robots to automate tedious (but necessary) tasks so you can focus on quality results and complex issues - at scale. When you build a pentest robot, you design a testing flow that chains our tools based on your know-how and approach. The resulting robot is a testing flow you can run automatically (Scan with Robot) against any target you want.
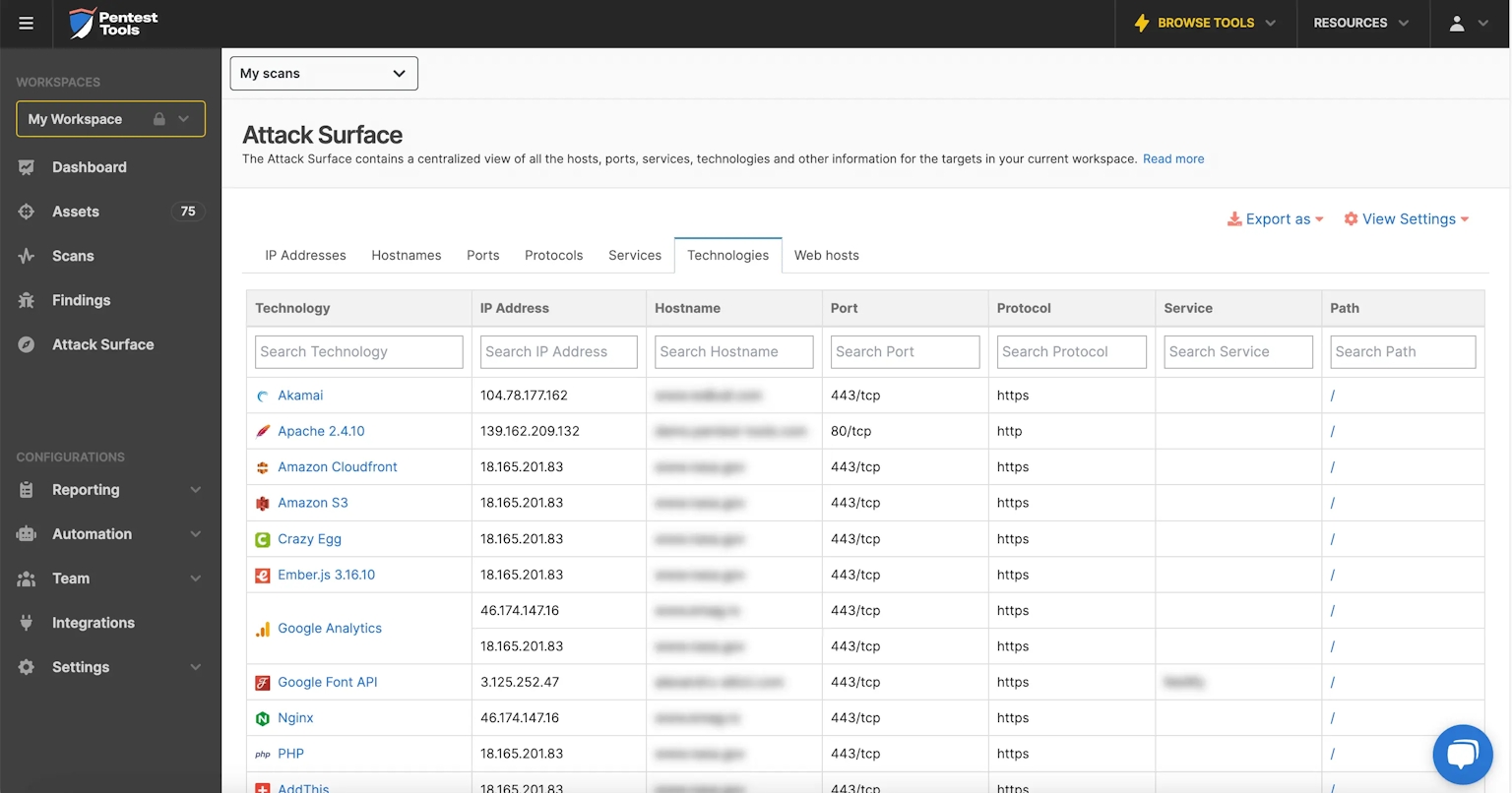
Discover Your Network's Attack Surface
Automatically detect open ports, services, and running software from all your targets. Visualize scan results in a unified, centralized view. The Attack Surface pulls results from Pentest-Tools.com scanners to give you an overview of your targets’ open ports, services, and other relevant details.
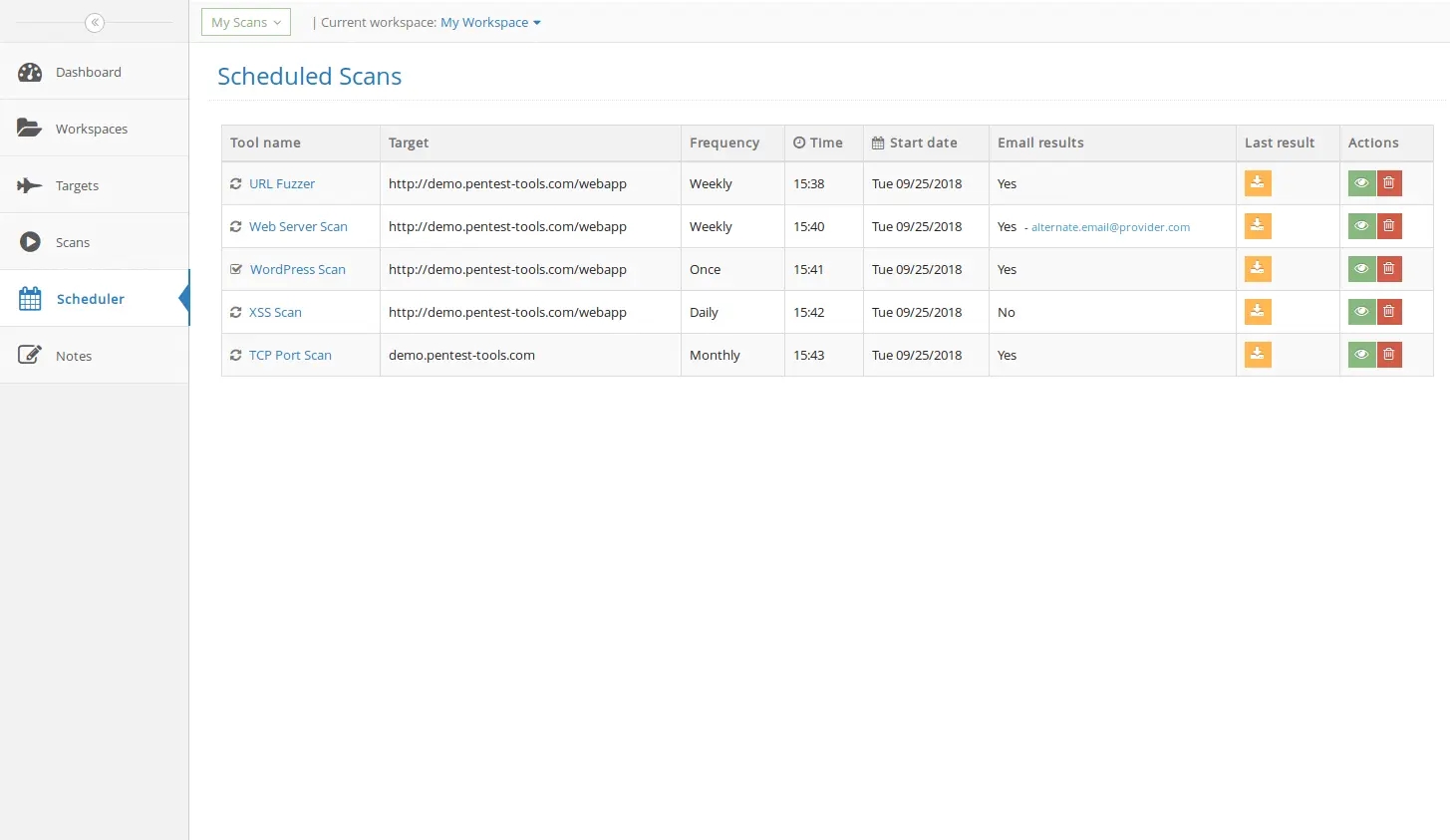
Schedule periodic scans
Continuously monitor the security of your systems and infrastructure by scheduling periodic scans. You can set them up to run daily, weekly, or monthly at a specific date and time. Get scan reports straight to your inbox or any email address of your choice.
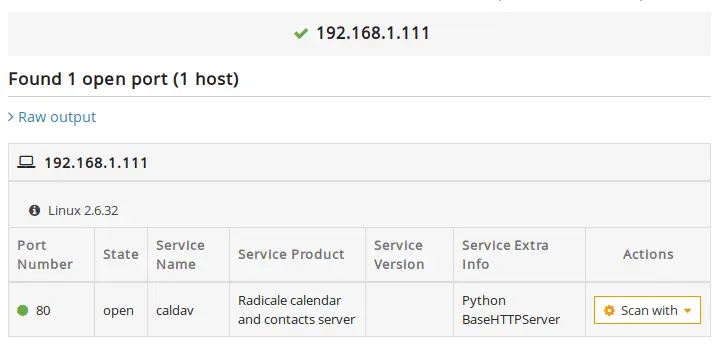
Internal network scanning through VPN
This feature lets you perform scans using VPN tunnels to reach internal networks or protected network segments. You can run any of our security tools through encrypted VPN tunnels to discover vulnerabilities from your internal network. Scanning through VPN also allows you to change the source IP of your scans to be accepted by your customer's firewall rules.
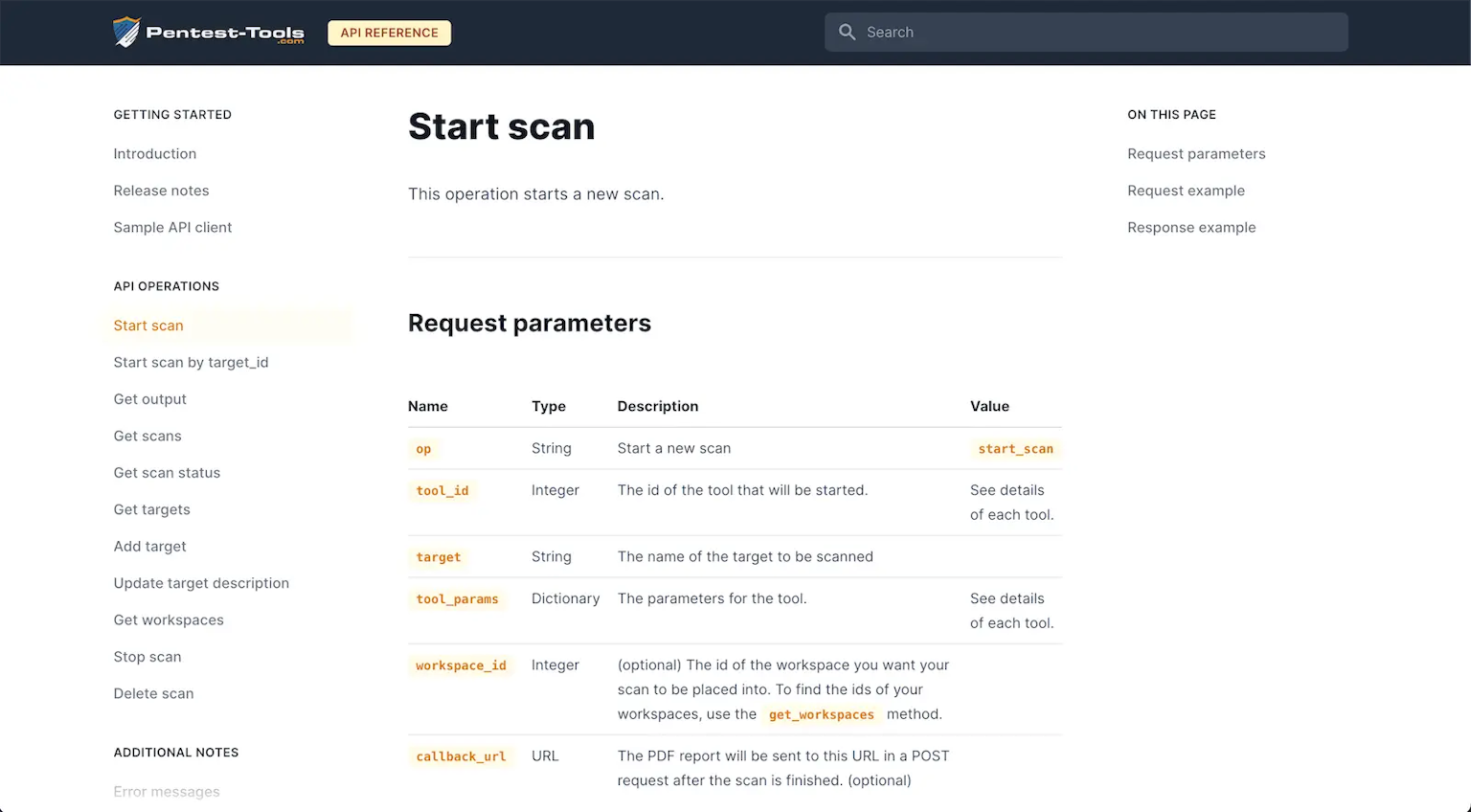
Access the tools programmatically using our API
The API allows you to integrate our platform with your tools and internal workflows. For instance, you can trigger automatic scans whenever you deploy a new website, or you make a change in your application. Furthermore, you can develop your own tools based on our scanning engines.
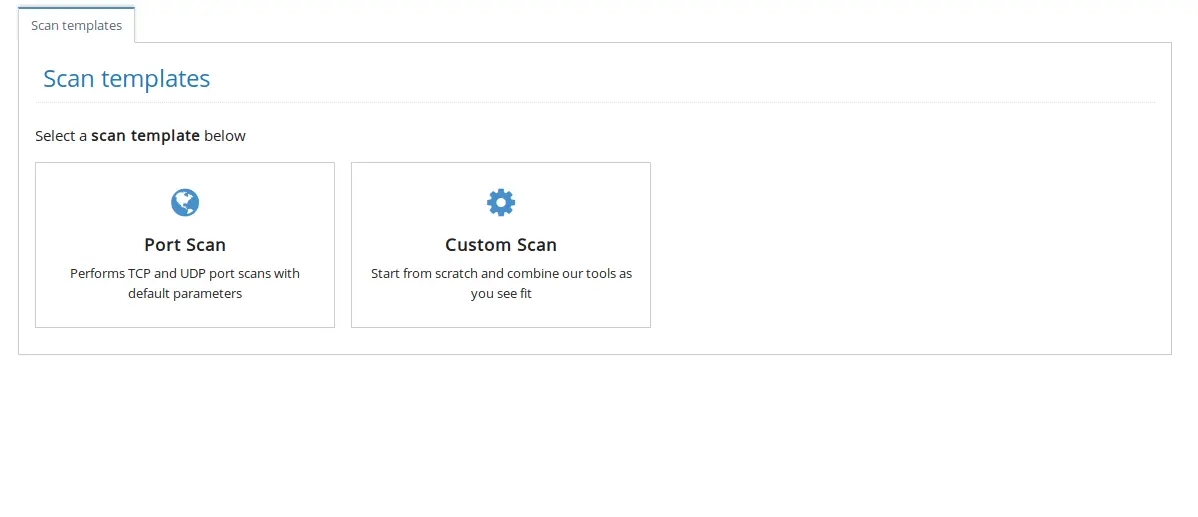
Scan Templates to run multiple tools against the same target
You don't have to manually run each scanner for the same target. With Scan Templates, you can group tools and options to start all at once for a target. Save valuable time and make your work more effective.
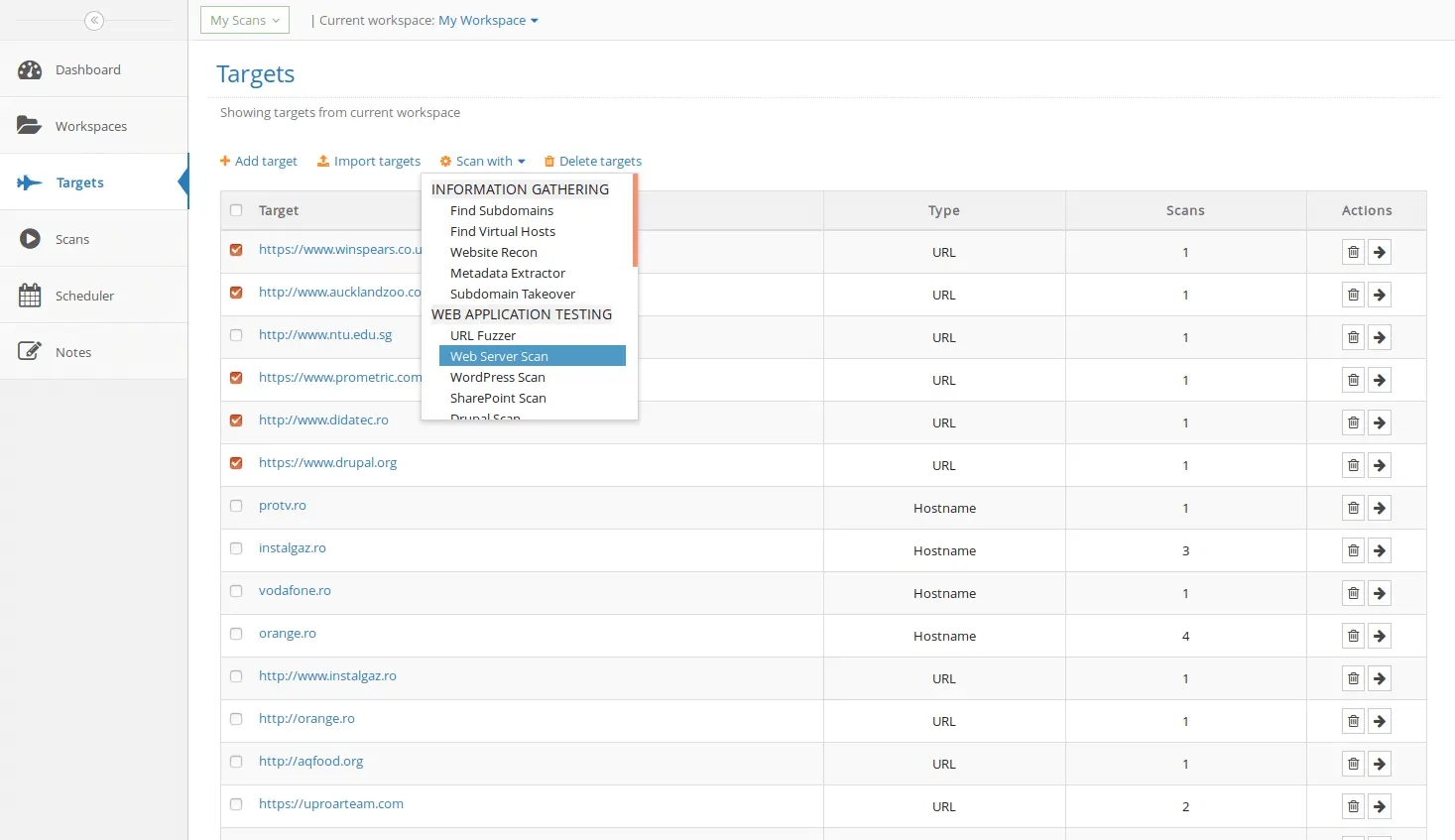
Scan multiple targets at once with Bulk Scanning
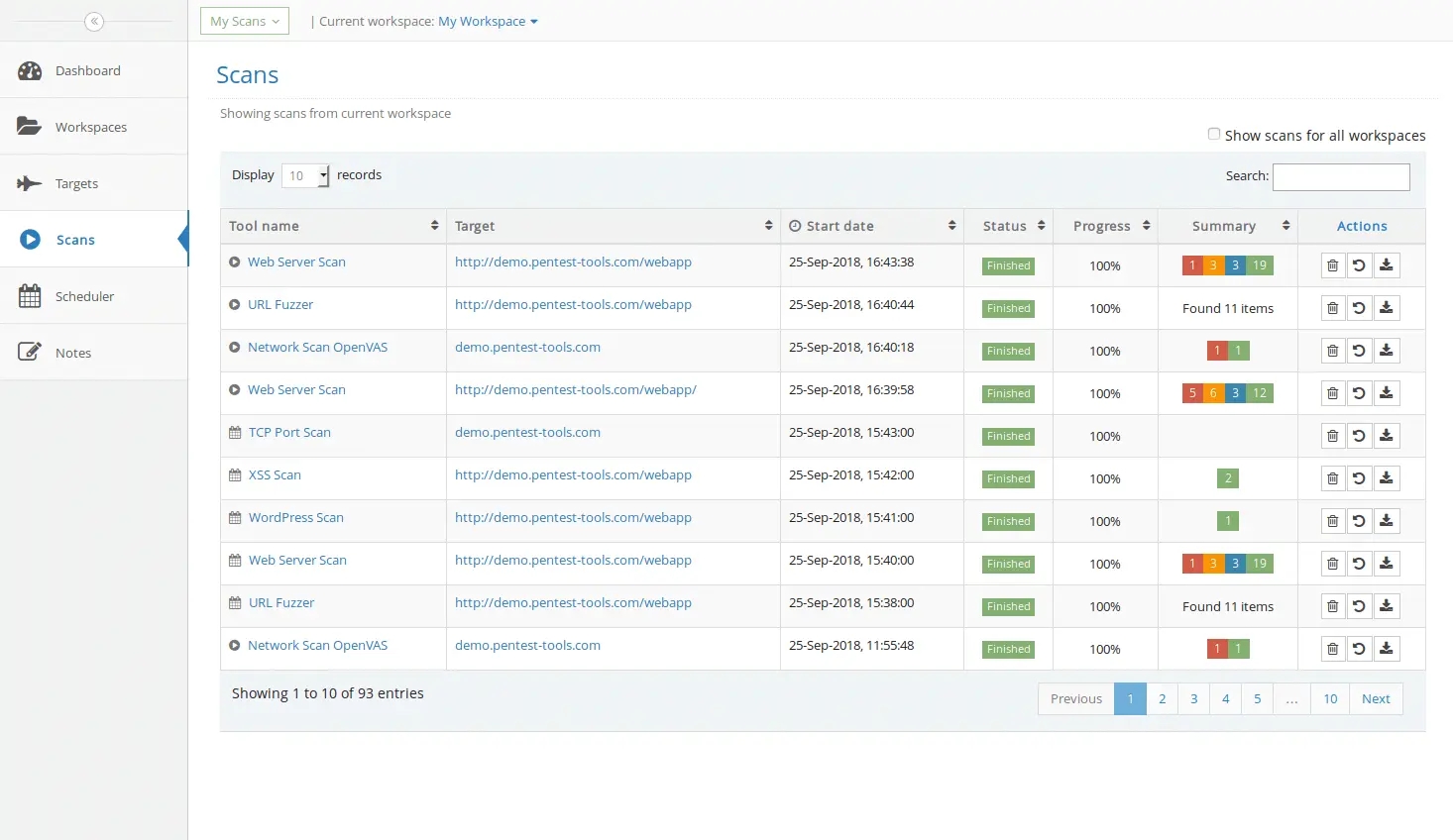
You can also select multiple targets that you want to scan and run a scanner against them. It starts a new scan for each target, which you can visualize in the Scans view.
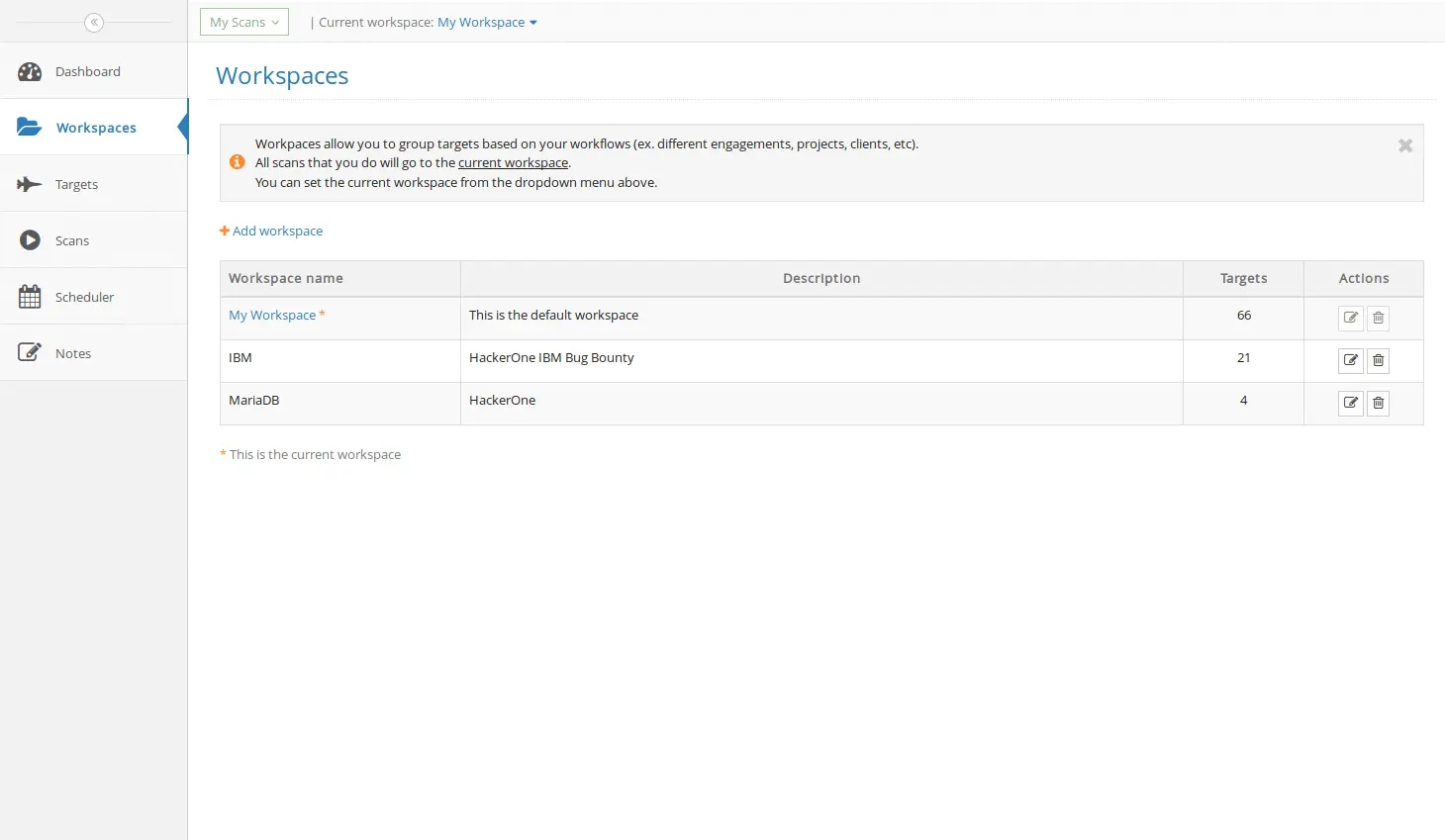
Organize your work with Shared Items & Workspaces
Workspaces are a good way to group your targets based on the project that you're working at, the client name, workflow, etc. All the work that you are doing goes into the current workspace (which can be set from the dropdown menu). However, you can move targets between workspaces and delete them if they are no longer necessary. You can also share any part of any workspace with your coworkers and members of the same master account.
Keep a history of your scans and compare them over time
Having a history of your scans allows you to see how the security of your targets has evolved. You can compare old results with new ones and see what has changed. Plus, you can choose to delete scan history permanently.